It started as a routine check-in between Umbrella Security and an anonymous office client.
A few minor issues. A couple cosmetic questions. Some system confusion.
Nothing urgent.
But within 60 minutes, it became clear the office didn’t have a security system problem.
They had a security clarity problem.
And that’s exactly what an effective office security assessment uncovers.
Access Control Integration: The Payroll Expectation Gap
The office wanted badge activity to integrate with their payroll system (we’ll call it TimeBridge Payroll Hub). On paper, it sounded simple:
• Employee badges in
• Time logs sync
• Payroll admin becomes easier
The time clock provider offered an “API kit.” But here’s the reality:
An API makes integration possible — not automatic.
When access control systems connect with payroll software, multiple stakeholders are involved:
• The access control system manufacturer
• The payroll platform provider
• Internal IT/admin
• HR and accounting
Without alignment across those parties, integration can stall for months — or never happen.
Security assessment takeaway:
Before promising integration, confirm data compatibility, vendor support, and implementation timelines.
The Door That Closed — But Didn’t Secure
Next issue: a garage entry door that appeared to close but didn’t always latch fully.
Staff had been reminding each other daily:
“Check the door behind you.”
That’s not a security feature — that’s a workaround.
After review, the likely culprit wasn’t “user error.” It was hardware interaction:
• Lock timing
• Strike alignment
• Door pressure
• Reader delay configuration
These are subtle issues that rarely show up in installation manuals — but they show up in real-world operations.
Security assessment takeaway:
If employees compensate for your security hardware every day, your system needs tuning.
Panic Buttons: Designed for Real Behavior
The office also had legacy wired panic buttons under desks. No one was entirely sure whether they were still active.
That’s a hidden liability.
The conversation shifted toward modern solutions:
• Discreet wireless panic buttons
• Wearable panic devices
• Fixed buttons in public-facing areas
• App-based panic activation via alarm system software
Then came the key insight:
In a real confrontation, no one is pulling out their phone calmly.
Effective panic protection must match human behavior under stress.
Security assessment takeaway:
Panic systems should be layered, flexible, and designed for how staff actually react — not how policies assume they will.
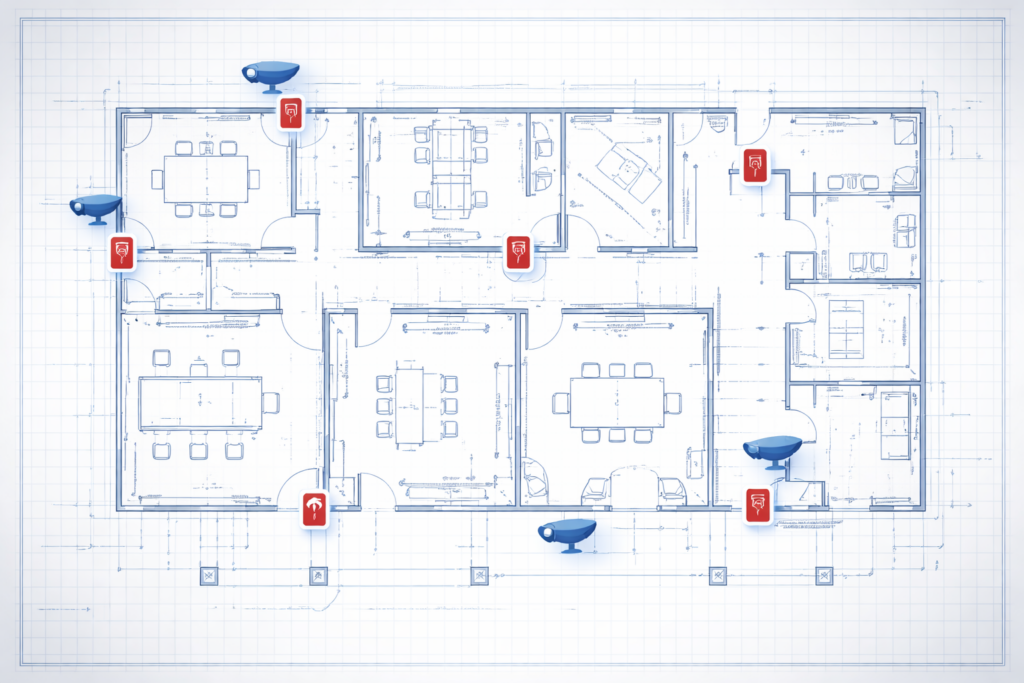
Cameras Installed ≠ Cameras Usable
The office had a functional camera system with video management software.
But they couldn’t reliably access footage from their computers.
The root causes were predictable:
• Remote client software not fully configured
• Firewall rules not finalized
• Admin permissions too broad on shared machines
• No training on searching, exporting, or reviewing footage
A camera system without clear access protocols is operationally weak — even if the hardware is high quality.
Security assessment takeaway:
Remote viewing, permissions, and training are as important as the cameras themselves.

The 2:00 a.m. Alarm Question
Then came the scenario every office eventually faces:
“If the alarm goes off at 2:00 a.m., what happens next?”
There was confusion around:
• Who receives monitoring calls
• Whether police dispatch triggers automatically
• Who confirms “all clear”
• What cancellation codes are used
• Whether follow-up calls occur
Monitoring only reduces risk when escalation procedures are crystal clear.
Security assessment takeaway:
Every commercial office should document its alarm monitoring procedure — including call hierarchy and response expectations.
The Real Lesson: Security Is an Operating System
By the end of the meeting, the office hadn’t just identified hardware issues.
They had identified process gaps:
• Access control expectations
• Door reliability
• Panic coverage
• Camera usability
• Alarm response clarity
That’s what a proper office security assessment delivers.
Not more devices.
More confidence.

Security Clarity Starts with the Right Assessment
If any of these scenarios sound familiar: unclear integrations, unreliable doors, outdated panic buttons, limited camera access, or alarm confusion it may be time for a structured security review.
Umbrella Security conducts practical, real-world office security assessments designed to identify operational gaps, not just hardware issues.
Schedule a commercial security assessment and gain clarity on how your systems are actually performing.